The first five steps
- Download Tor Browser
- Copy a verified Wethenorth address
- Check the PGP canary
- Register or sign in
- Enable two-factor PGP
Get you to your dashboard safely.
Your first visit
Eight steps to safely reach the market from zero knowledge. Twenty minutes end to end if this is your first time. No shortcuts, just clarity.
The roadmap
Five core steps to reach Wethenorth, plus three additional security layers that matter. The first five get you logged in. The last three keep your account and coins from leaving your control.
Get you to your dashboard safely.
Keep you in control of your funds.
Step by step
Download the current release directly from torproject.org over HTTPS. This is the only browser that connects to .onion addresses, and the only safe way to reach Wethenorth.
The signature check is a three-line command if you have GnuPG installed. Compare the downloaded file against the Tor Project signing key. If your signature verifies, you know the installer has not been compromised in transit.
Installation is straightforward. On Windows the installer places Tor Browser in a portable folder. On macOS it drops a standard app bundle. On Linux you unpack the archive to any location and run the start-tor-browser script. The first launch takes longer than later ones because Tor builds a fresh profile and joins the network — two minutes on typical broadband is normal.
If you run Tails from a USB, Tor Browser is already included and kept up to date. Mullvad VPN users running a separate VPN: the market does not expect Tor-over-VPN and has no preference — consult the FAQ below if you want the technical reasoning.
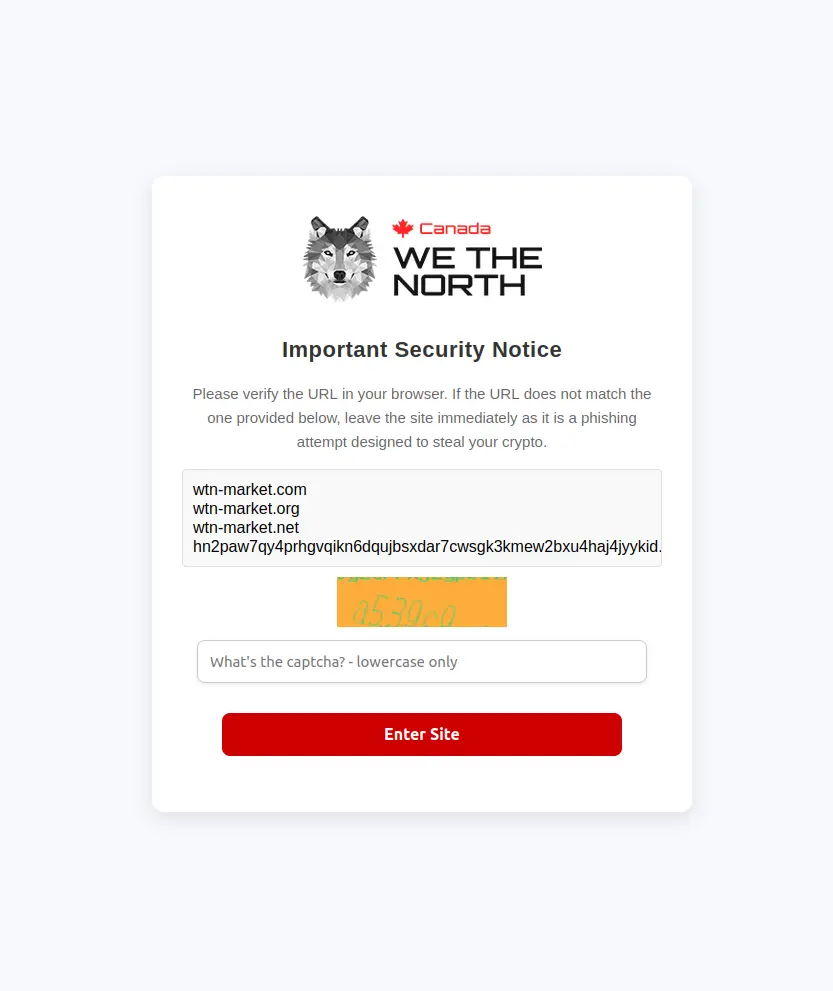
Use the Copy button next to the primary address on the home page. Paste it whole into the Tor address bar. Never type it manually because v3 onion addresses contain 56 characters and one mistake opens a phishing clone that looks identical.
The 56-character length is cryptographic. Each character is part of a signature of the server's public key, proving to your Tor client that you reached the correct hidden service. One wrong digit does not open a "similar" market — it opens a different machine entirely. If that machine was set up by a phishing operator, the interface will look identical while they log your credentials.
A common habit among regulars is to paste the address into a text editor first, count the characters, and visually scan the first six and the last six. The middle is hard to verify by eye, but phishing clones usually change the opening or closing block because those are what users remember.
Before logging in, check the canary link from the home page login banner. Compare the signature date. If it is older than eight days, stop and wait for an update.
The canary is a short statement signed with Wethenorth's private PGP key. It declares that no warrants have landed and no staff member is compromised. A healthy market refreshes it weekly. The eight-day rule is a rolling grace window — servers miss a day for maintenance, so "stale after eight" avoids false alarms while still catching real silence.
Import the admin public key once, from the pinned post on dread under /u/wethenorth, then keep it on your daily machine. Checking a canary afterward is a single GnuPG command and takes under a second.
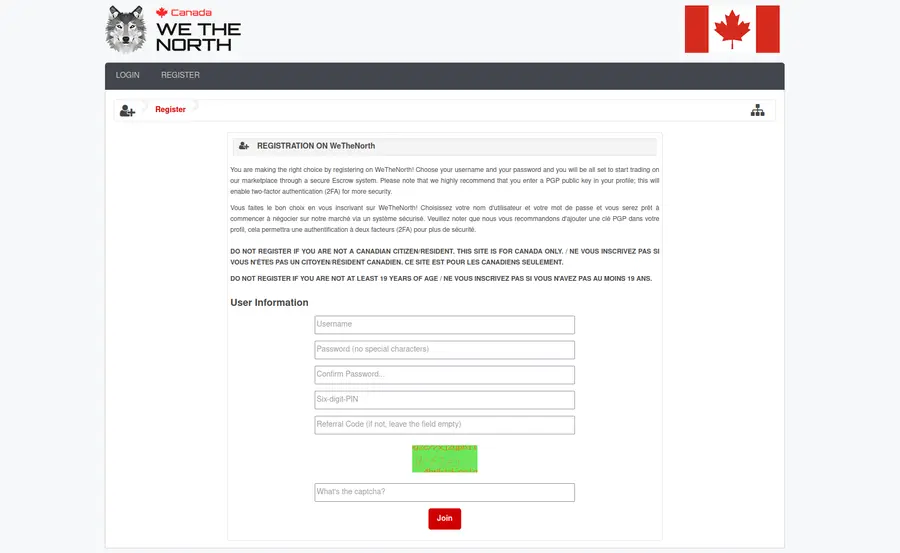
New accounts need a username, password, and a six-digit PIN for withdrawals. Do not reuse credentials from any clearnet service, including email. Credential reuse is the single most common mistake on any darknet market.
A database leak from a forgotten clearnet forum ends up with attackers trying the same email-password pair on every market. Accounts that reuse those credentials drain overnight. Pick a username with no link to anything you post elsewhere. Generate the password in your password manager — 24 characters or more, random — and store it there.
The withdrawal PIN is separate from login password on purpose. Even if someone reads your password in transit, they still need the PIN to move coins off the account. Email signup is optional. Most regulars skip it since email creates a weak link between your market account and a clearnet identity. If you do provide one, use a throwaway address from Proton Mail set up over Tor.
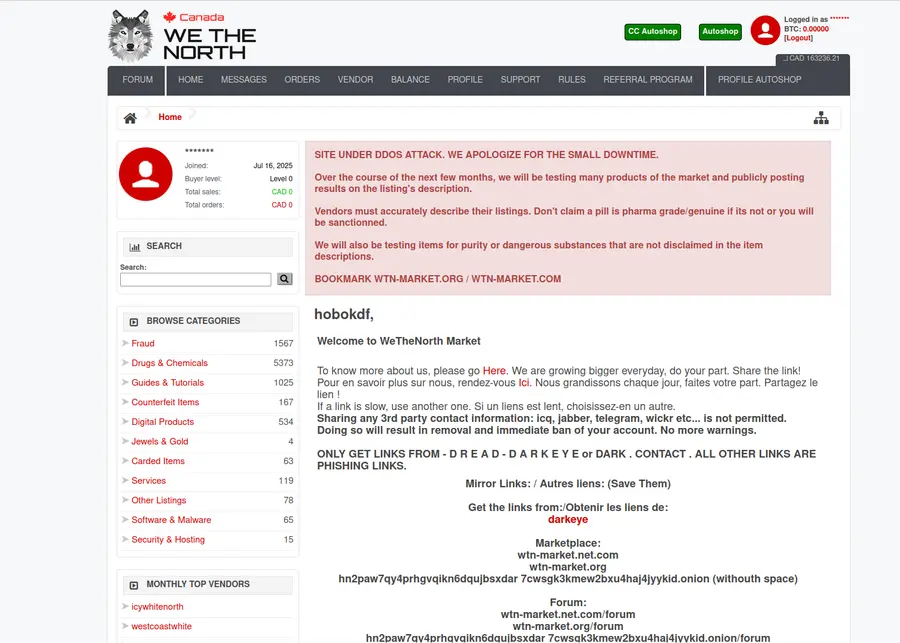
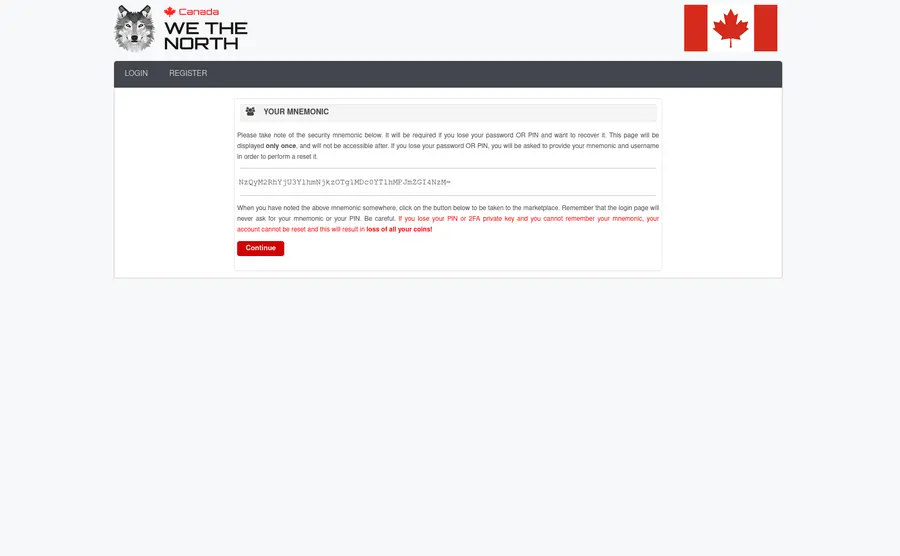
Add your public PGP key in account settings. From that point every login requires you to decrypt a short challenge, which blocks password-only takeovers. This is the step most new users skip, and the one that saves most regulars when something goes wrong elsewhere.
Generate a key pair on your local machine with GnuPG. Copy the public block into your account settings. Save the private key somewhere you control. From that point the login flow shows a block of ciphertext that your private key decrypts to a one-time string. Paste the decrypted string back into the page and you are in.
Someone who steals only your password sees the challenge and stops — they cannot proceed without the private key. Do not keep the private key on a machine you share. A Tails USB is the cleanest option. A hardware token works well if you prefer something more portable. For vendor communication, the same key encrypts address labels and shipping details.
Wethenorth uses invite-only registration. New accounts require an invitation from an existing member in good standing. This system limits the user base but significantly reduces law enforcement infiltration risk.
Look for invitation requests in dread forum threads related to Wethenorth. Established community members occasionally share invites with verified newcomers. The Dread platform is where all Wethenorth discussions happen, including official announcements from the /u/wethenorth account.
Building reputation in the community first — participating in relevant discussions, asking informed questions — increases the likelihood that established members will vouch for you. The invite-only system exists because open registration allows anyone, including law enforcement, to create accounts and monitor the platform.
Get BTC or XMR through a legitimate exchange. Withdraw to a self-custody wallet — Cake Wallet for Monero, Electrum or BlueWallet for Bitcoin. Never transact from an exchange wallet.
Monero provides maximum privacy with untraceable transactions. Bitcoin is more widely held. For Monero, Cake Wallet is straightforward on mobile and desktop. For Bitcoin, a self-custody wallet with coin-control gives you full privacy. Avoid exchange wallets for anything market-related because exchanges monitor outgoing withdrawals.
Generate a fresh deposit address for each order. Keep the seed phrase temporarily inaccessible on paper. Never consolidate change outputs and never mix coins from different sources. Chain analysis on small domestic amounts is weaker than on international transfers, but it still rewards basic precautions.
For deeper reading on wallet security, Blockchain explorer shows how transactions work on the public ledger. Binance Academy has readable primers on cryptocurrency security fundamentals.
Browse listings by category. Read vendor feedback carefully — stealth rating, shipping speed, and response time are the three signals that matter. Start with a small order to test the vendor and the postal system.
Communication with vendors should follow a standard approach. PGP-encrypt anything that contains an address or a phone number. Sign the message so the vendor knows it was you. Keep clearnet out of it entirely. The order page message thread is the only channel that travels with the dispute record — use it for anything a dispute might later reference.
Escrow is mandatory for new accounts. Default escrow runs for seven days after the vendor marks the order as shipped. Buyers can extend by another seven days if the package has not arrived. Wethenorth's domestic Canadian shipping means packages move through Canada Post and standard couriers — delivery windows are consistent with legitimate domestic parcels.
For adjacent conversations with people you already trust, Matrix Protocol and Jitsi Meet are fine. But keep the order page thread as your primary channel for anything with legal consequences.
Custody & privacy
Your coins are only safe if you control the private keys. Exchange wallets are not your coins — the exchange is. Self-custody wallets give you full control and full responsibility.
Monero transactions are untraceable by default. Every transaction hides the sender, receiver, and amount using ring signatures and stealth addresses. Most regulars use Monero for this reason.
Always generate wallets on an temporarily inaccessible machine if possible. Back up the seed phrase on paper.
Bitcoin is pseudonymous. Transactions are transparent on the blockchain. Privacy requires care: fresh addresses, no change consolidation, coin control. Some vendors accept a small discount for Monero.
Use the Blockchain explorer to understand how your transactions appear on the public ledger.
Operational security
Tor alone is sufficient and what Wethenorth expects. Running Tor-over-VPN adds complexity and can create fingerprinting vulnerabilities. If you want a VPN for your ISP, Mullvad is the one regulars tend to trust. But it is not required.
Public WiFi exposes you to traffic inspection and key logging. Tor Browser running on public WiFi is still relatively safe because Tor is encrypted end-to-end. But do not enter credentials or send cryptocurrency addresses over public WiFi without Tor. Mobile phones logged into social media are fingerprinting vectors. The best practice is a dedicated temporarily inaccessible device for cryptocurrency and PGP key storage.
Wethenorth orders ship through Canada Post and domestic couriers. Canadian postal inspection requires a warrant. Packages that arrive look identical to legitimate domestic parcels — no "suspicious" markings because nothing crosses a border. This is why domestic shipping is the market's core advantage.
Tails is a live operating system focused on privacy. Boot Tails from a USB, do your market activity, ceased operations, and nothing is written to permanent storage. For serious OPSEC, Tails is the baseline. I2P is a parallel anonymity network if you want additional reading on alternatives.
Every message to a vendor that contains a payment address, shipping details, or personal information should be PGP-encrypted and signed. Use the same key you uploaded to your Wethenorth account. Keep communications inside the order page message thread, which is the only place a dispute moderator will see the full conversation.
Common questions
Downloading Tor and reaching the login page takes ten minutes. Registering and setting up PGP two-factor takes another ten if you already have a cryptocurrency wallet. Total: twenty minutes if this is your first time and you are not distracted. If you are setting up wallets and PGP from scratch, budget an hour.
You can skip steps one through five. Log in normally. Step six (obtaining an invitation) does not apply if you already have an account. Steps seven and eight (wallet setup and first order) are good practice refreshers if you have not used the market in a while. The security practices in the section above apply whether you are new or returning.
Accessing the marketplace and browsing is not illegal. What you do on the marketplace is your responsibility. Canadian federal law covers the Controlled Drugs and Substances Act, fraud, theft, and various other offences. This guide is informational only and does not constitute legal advice. Consult a lawyer if you have specific questions about what is legal in your jurisdiction.
Yes. Password managers are good security practice because they generate strong, unique passwords and keep them encrypted. Use your password manager to generate a 24+ character password for your Wethenorth account. Store the withdrawal PIN separately if your password manager does not support separate fields. The two-factor PGP challenge still protects your account even if the password is stolen.
You can disable PGP two-factor from your account settings. You will need your password and withdrawal PIN. Once disabled, you can log in with password alone and generate a new PGP key pair. This is why the withdrawal PIN is separate — it gives you a way to recover the account even if the PGP key disappears. Back up your private key on paper or a dedicated USB so this does not happen.
Three checks: First, verify the .onion address against the one on this page — count the characters if you have to. Second, check the PGP canary on the login page — a phishing clone cannot serve the signed canary because it does not have the private key. Third, try to log in. If your credentials work on a clone, you know it is fake and you should not proceed. Change your password immediately on the real Wethenorth.
Yes. Tor Browser runs on iOS and Android. Download it from the official source, not a third-party app store. Mobile phones are generally less secure than desktops for OPSEC because they collect more data about your location and behavior. For best security, use a dedicated device or Tails for market activity.
The PGP canary is updated weekly. If it is older than eight days, the market may be under a warrant and the admins cannot say so publicly. The eight-day grace window avoids false alarms from a skipped maintenance day. If the canary is more than eight days old, wait for an update before using the market. If the canary disappears entirely, wait for confirmation on dread before logging in.
Ready to start?
Go back to the home page. Download Tor Browser. Copy a verified address. Check the canary. Register. Enable two-factor. Set up your wallet. Make your first order. That is it.
Return to home pageQuestions? Check the quick answers section on the home page or read the background page.